The Virtual Machines and Virtual Network map for the Password Security... | Download Scientific Diagram

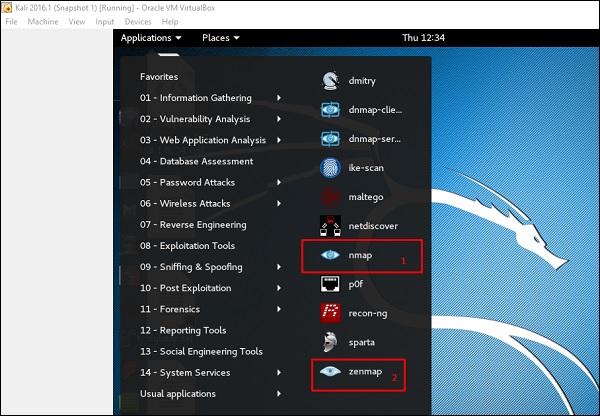
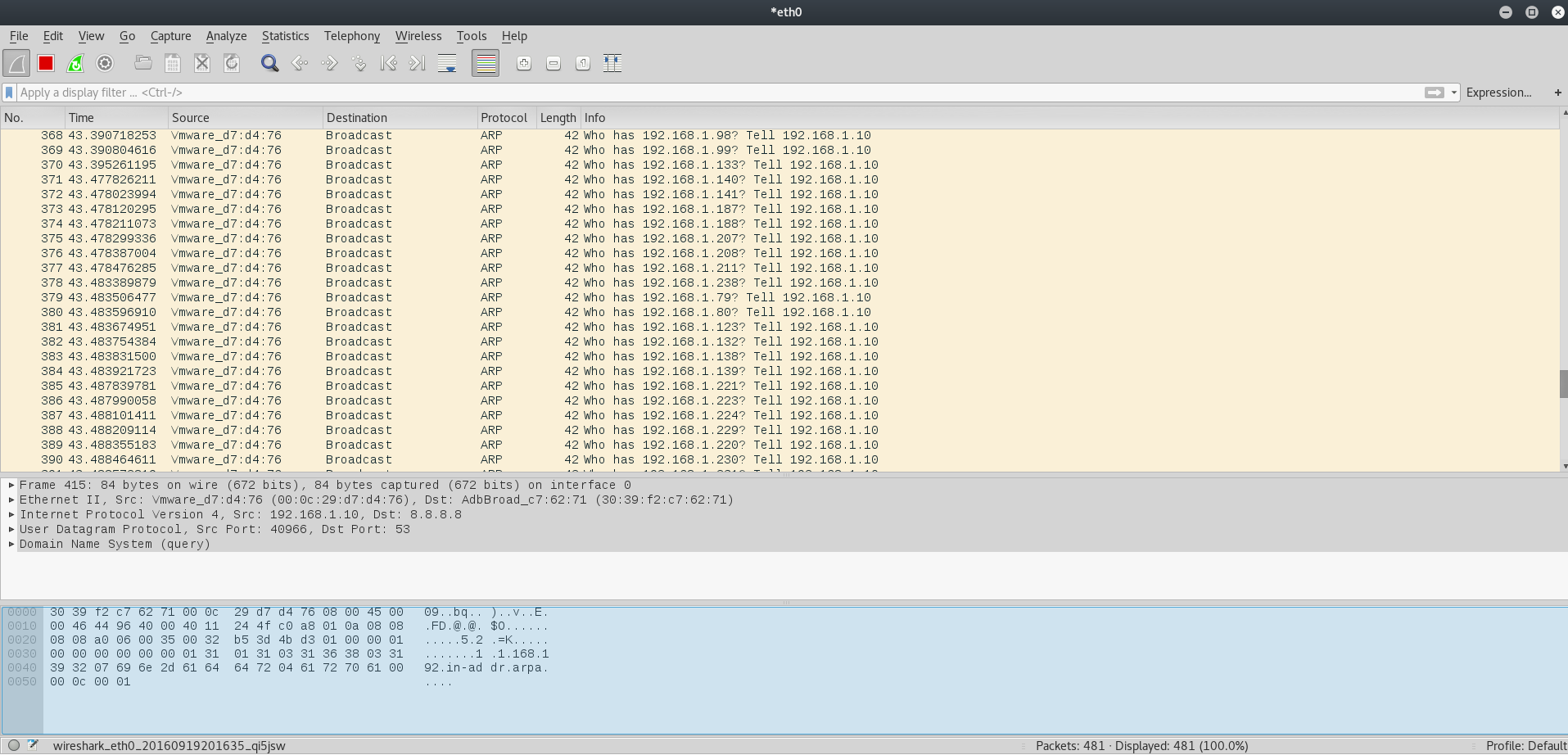
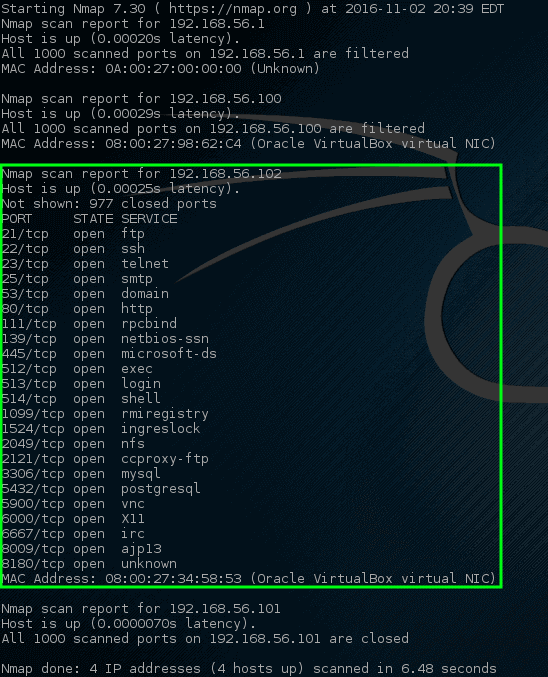
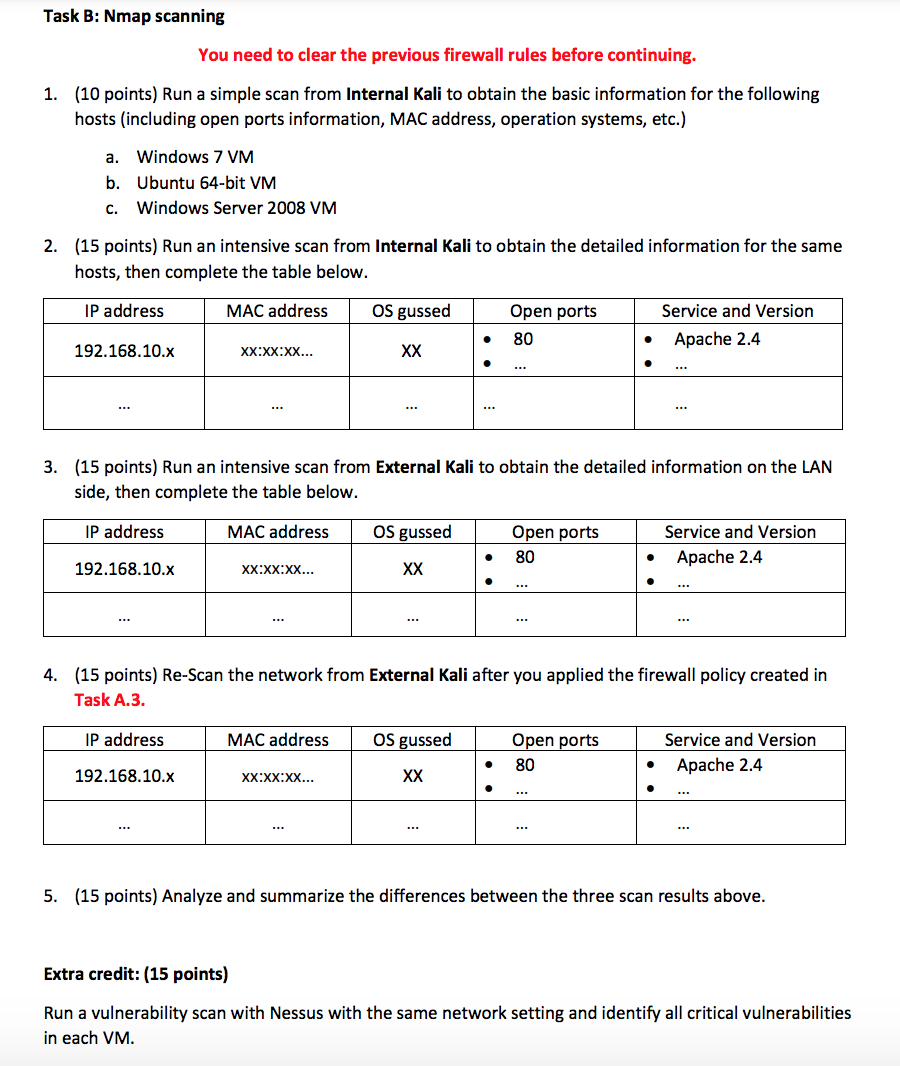
Kali Linux Tutorials on Twitter: "World Wide Live Attack Map & Analytics http://t.co/gdtWyAJMwa http://t.co/OqIqv69h9x" / Twitter

Mapping Digital Drainage Network Using Geoprocessing: A Case Study of Kali Gandaki River Basin, Nepal Himalaya | Semantic Scholar




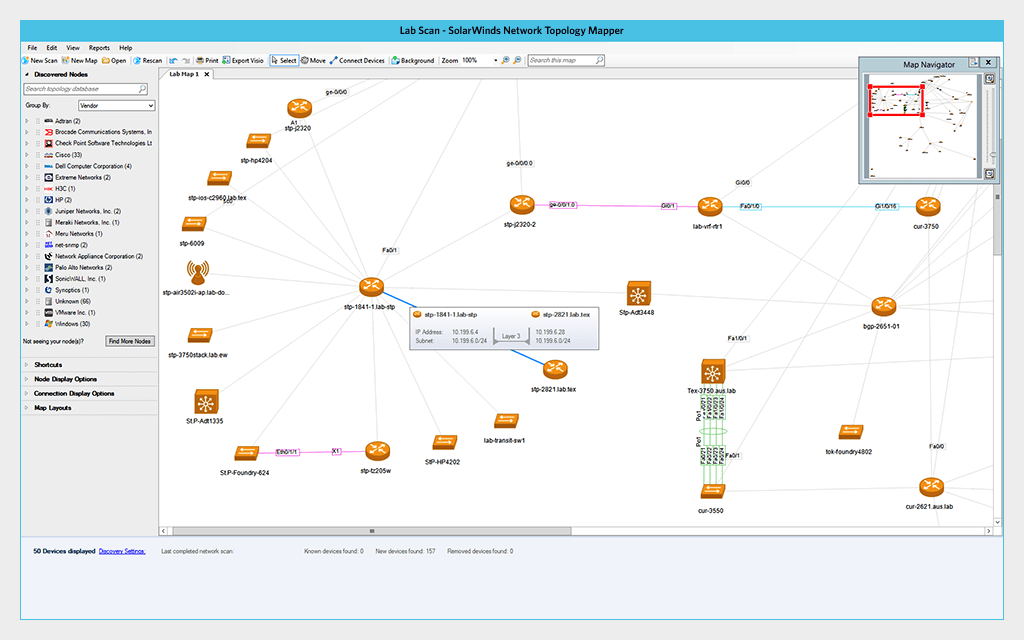




![7 Best Network Mapping Software [Updated for 2022] - DNSstuff 7 Best Network Mapping Software [Updated for 2022] - DNSstuff](https://www.dnsstuff.com/wp-content/uploads/2019/09/Network-Performance-Monitor-2-1024x640.jpg)